
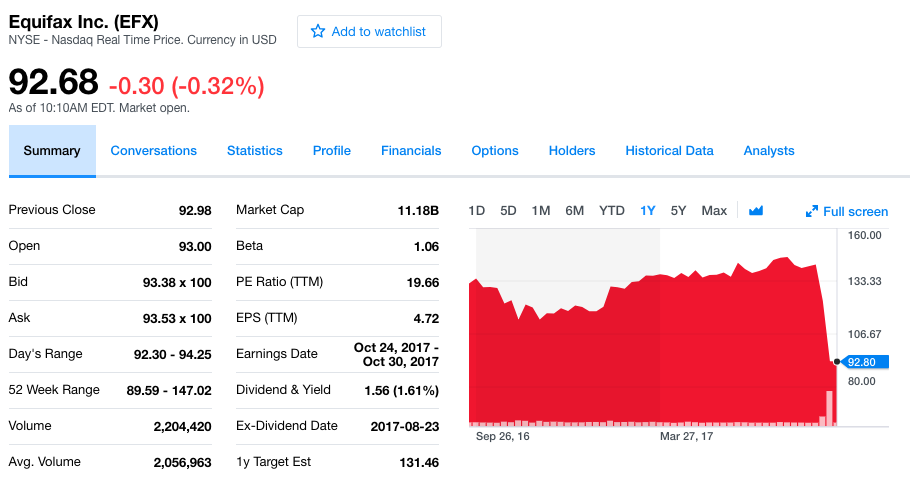
Late last week (around 9/15/2017) it was reported that the CIO and CSO at Equifax “resigned”. Equifax stock is down by around 30%. The FTC is launching an investigation and findings and settlements are likely to be in the $100’s of millions or more. Clearly there are going to be short and medium term impact to Equifax’s security bumbling. In this post, we’re going to present a longread with our thoughts about Equifax.
One of the first reactions people had was to talk about this Atlantic article and ask the question: “Isn’t our data already out there? What can we actually do?”
Consumer data breaches have become so frequent, the anger and worry once associated with them has turned to apathy. So when Equifax revealed late Thursday that a breach exposed personal data, including social-security numbers, for 143 million Americans, public shock was diluted by resignation.
I think this article is bordering on irresponsible. Yes, your data may be out there. Yes, you should not be shocked by another breach. But absolutely, it is incumbent upon us to watch our credit and work to improve security so that this doesn’t continue to be expected.
There is a term I like to use for where we are as an industry: technical debt. In Agile development projects, technical debt is the term we use for work we put off in order to get the main project done faster. It could be something like testing, or refactoring to ensure we are building a more robust system. We know we’re prioritizing delivering the system and cutting some corners. Those corners we cut are technical debt that we may have to circle back and do. Often this happens (we circle back and deal with debt) when a company gets acquired or partners with a larger firm. Many times, this technical debt never actually gets paid back. I would argue that in most corporations, the vast technical debt waiting to be paid off represents one of the biggest overall security issues.
Another way to look at this is through the lens of budgets. If a company increases its IT budget 5% each year, it may seem to be growing and investing. After 20 years, if the IT Security Budget starts to grow at a pace of 2x the regular IT budget (so 10% each year) then the leadership of a company feels that they are being aggressive and strongly supporting security. But from a security perspective, we were underinvesting all along so even incremental 10% increases in budget are leaving us woefully underinvested to truly provide security.
We need to be able to come up with an independent model for what we should be doing for security and then fund the right work. Usually that’s going to cost a lot more than people want.
Consumers can do a lot to keep themselves safe – but it will be a fair amount of work and takes time, energy and money.
The FTC following this is a good sign for consumers because it suggests that Equifax and other companies handling this type of data will expect to see punishments (fines) that are likely to spur them to invest more in security.
Far be it from me to say this – but it is possible that the whole credit reporting system should be re-envisioned. Not to mention identity and SSN.
For companies, some key takeaways from the Equifax breach include:
If we address security from the beginning and as a first class part of every project, we can design for security, test for security, write requirements for security and ultimately deliver more secure applications.
As incidents like Equifax show, consumers and regulators expect us to be thinking about privacy and security.
A significant part of Jemurai’s business is trying to help companies reshape their application delivery to be secure. Every client is different. But we see a surge in demand for security that is only increasing.
From what we can tell, the root issue was an application built with an old version of Struts. So the immediate action Equifax could have taken would have been to keep their libraries up to date. Of course, whenever the answer is “to patch” it suggests an underlying vulnerability that is interesting in its own right.
Behind the immediate action of staying up to date, the vulnerability had to do with remote code execution. In layman’s terms, that means the vulnerability allowed a user to get code to run on the server. There are a variety of ways that this happens in the real world these days … sometimes people take strings (a bunch of characters) and process those without checking that they fit certain rules.
For more detail, check out our previous blog post and video.
Another swirling discussion has been about the CSO who’s LinkedIn page cited a music degree as qualifications. Many folks questioned that as a qualification. I think this is basically a red herring argument. The CSO may have been qualified and may not have been qualified, but the academic background is unlikely to have factored in the result. Many great programmers come from music backgrounds – it is actually something some companies look for.
The more important question here is how the Equifax CEO and Board have responded to requests for funding for security.
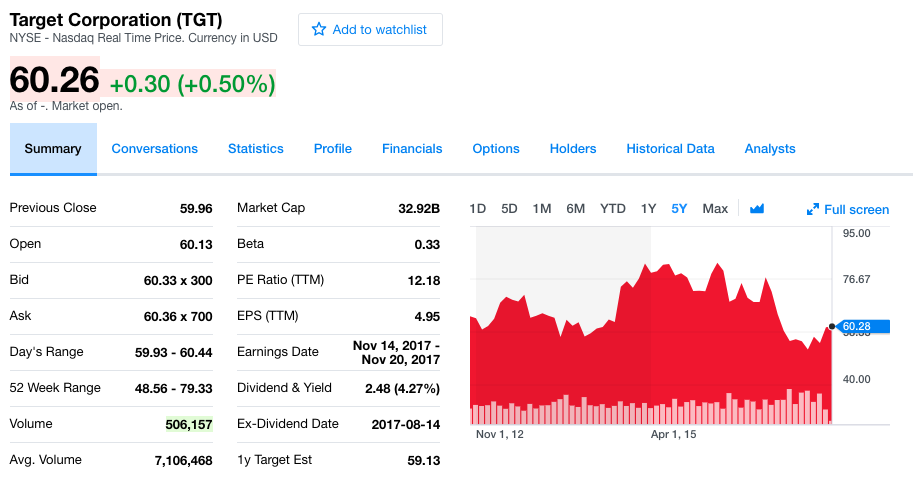
It is very hard to say what the long term impact of the Equifax breach will be. In the case of Target, if we look at the stock chart it is hard to even know when the infamous breach occurred. If we look closely we can see a dip around December 2013 but changes in the stock price are largely unrelated to security events and it certainly didn’t destroy the value of the company the way many thought that it might.
Equifax on the other hand, is at least in some sense specifically responsible for consumer’s security. There could be no doubt that Equifax had sensitive data that would be coveted by schemers. It is possible that they will held accountable to a different standard than was Target. I wouldn’t hold my breath.
As humans, it is natural to simplify events, imagine them as a game and maybe even as having an end or closure. So, if this is the end of the game, I would say that the score is Equifax 213 – Hackers 25.
Equifax has still been commercially doing a lot for its shareholders. It is most likely to continue to see success as a business. On some level, Equifax is still winning.
On other hand, this is a very significant breach. Nobody probably would have thought that the Equifax attackers could get 25 points. That might represent a surprising vulnerability. Regulators will likely add to that opposing score as they impose oversight and fines.
In order to protect their lead, Equifax is going to need to spend a lot more money and time ensuring they don’t give up more scores. The game may slow down. The profit may decline. This will probably have ripple effects with their immediate competitors as well.
In the scheme of things, it is a test of all of our collective will to improve and sacrifice. If we can envision better systems for identity and more inherently secure systems for credit scoring (blockchain anyone?), there are opportunities to dramatically improve security while realizing the benefits of a continually more technology advanced and connected world.
Of course, the game will go on. Equifax may give up a lot of points, but if they keep their business running – it is likely that they’ll still come out with a higher score and “win”. In some ways, I just hope the game isn’t that much fun to watch.