We spend a fair amount of time building and using OWASP Glue to improve security automation at clients. The idea is generally to make it easy to run tools from CI/CD (eg. Jenkins) and collect results in JIRA. In a way, Glue is like ThreadFix or other frameworks that collect results from different tools. Recently, we thought it would be cool to extend some of what we were doing to AWS. We have our own scripts we use to examine AWS via APIs but we realized that Scout2 was probably ahead of us and it would be a good place to start.
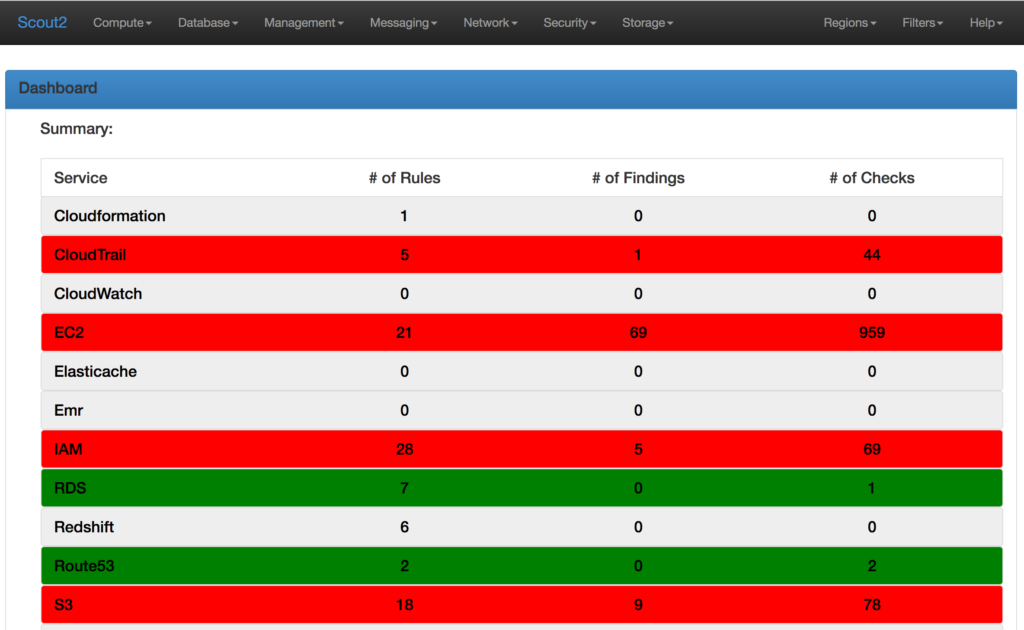
The fine folks at NCCGroup wrote and open sourced a tool for inspecting AWS security called Scout2. You can use it directly, and we recommend it, based on the description here: https://github.com/nccgroup/Scout2. It produces an HTML report like this:
For most programmers, running Scout2 is easy. It just requires a little bit of python setup and an appropriate AWS profile. So it wasn’t so much the barrier to entry that made us want to integrate it into Glue so much as the idea that we could take the results and integrate them into the workflow (JIRA) that we are using for other findings from other tools. We thought that having an easy way to pull the results together and publish them based on Jenkins would be pretty useful.
Glue has been a fun project that we’ve used opportunistically. The next set of goals with Glue is to clean it up, improve tests and documentation and prepare for a legitimate 1.0 release. At that point, we’ll probably also try to get Glue submitted for Lab status as an OWASP project.